Russian hackers have learnt to extort money for locked iPhone

The exact number of hacked phones is unknown. The representatives of Apple declined to comment.
The attackers use the fact that in the new version of iOS 7 has become possible to block stolen smartphone that cannot be removed with help of a reset or flashing devices. If you want to use this feature, you must know the user‘s name (Apple ID, also known as e-mail address) and password.
TrueCrypt for Windows: No major flaws found in first phase of security audit
 The first round of results are in, and so far TrueCrypt, the popular open-source encryption program, has a relatively clean bill of health. Security firm iSec Partners recently carried out the first phase of the TrueCrypt audit on behalf of the Open Crypto Audit Project (OCAP).
The first round of results are in, and so far TrueCrypt, the popular open-source encryption program, has a relatively clean bill of health. Security firm iSec Partners recently carried out the first phase of the TrueCrypt audit on behalf of the Open Crypto Audit Project (OCAP).
OCAP is the official name for the group behind istruecryptauditedyet.com, a project inspired by the revelations about the National Security Agency’s surveillance activities. OCAP was created by Matthew Green, a cryptographer and research professor at Johns Hopkins University, and Kenneth White, Principal Scientist at Social & Scientific Systems. For its report, which was released on Monday, iSec took a look at TrueCrypt’s latest Windows edition (version 7.1a).
Read moreGalaxy S5 fingerprint scanner hacked with glue mould
 The fingerprint sensor on Samsung's Galaxy S5 handset has been hacked less than a week after the device went on sale.
The fingerprint sensor on Samsung's Galaxy S5 handset has been hacked less than a week after the device went on sale.
Berlin-based Security Research Labs fooled the equipment using a mould it had previously created to spoof the sensor on Apple's iPhone 5S.
The researchers said they were concerned that thieves could exploit the flaw in Samsung's device to trigger money transfers via PayPal. The payments firm played down the risk. "While we take the findings from Security Research Labs [SRL] very seriously, we are still confident that fingerprint authentication offers an easier and more secure way to pay on mobile devices than passwords or credit cards," it said.
Read moreThe Russian government refused iPad
 Government of Russia has refused iPad in favor superseding tablets Samsung, said the head of the Ministry of communications of Russia Nikolay Nikiforov.
Government of Russia has refused iPad in favor superseding tablets Samsung, said the head of the Ministry of communications of Russia Nikolay Nikiforov.
"It is protected in a special way devices that can be used for handling of confidential information.
Some information in the government sessions are confidential, and these devices (Samsung) fully meet these requirements and have passed the most stringent certification system" - quoted Mr. Nikiforov Agency ITAR-TASS. The Official reason "replacement" called a purely technical nature, that is, supposedly, the policy is not satisfied exclusively by the technical capabilities of equipment
Read moreGoogle, Facebook, Microsoft, Yahoo release details of US government data requests
 Facebook, Microsoft, Yahoo and Google on Monday began publishing details about the number of secret government requests for data they receive, hoping to show limited involvement in controversial U.S. surveillance efforts.
Facebook, Microsoft, Yahoo and Google on Monday began publishing details about the number of secret government requests for data they receive, hoping to show limited involvement in controversial U.S. surveillance efforts.
The tech industry has pushed for greater transparency on government data requests, seeking to shake off concerns about their involvement in vast, surreptitious surveillance programs revealed last summer by former spy contractor Edward Snowden. The government said last month it would relax rules restricting what details companies can disclose about Foreign Intelligence Surveillance Act (FISA) court orders they receive for user information.
Read moreGoogle may ditch 'cookies' as online ad tracker
![]() Google is developing an anonymous identifier for advertising, or AdID, that would replace third-party cookies as the way advertisers track people's Internet browsing activity for marketing purposes.
Google is developing an anonymous identifier for advertising, or AdID, that would replace third-party cookies as the way advertisers track people's Internet browsing activity for marketing purposes.
Google, the world's largest Internet search company, is considering a major change in how online browsing activity is tracked, a move that could shake up the $120 billion digital advertising industry. Google, which accounts for about a third of worldwide online ad revenue, is developing an anonymous identifier for advertising, or AdID, that would replace third-party cookies as the way advertisers track people's Internet browsing activity for marketing purposes, according to a person familiar with the plan.
Read moreHow the NSA accesses smartphone data
 The US intelligence agency NSA has been taking advantage of the smartphone boom. It has developed the ability to hack into iPhones, android devices and even the BlackBerry, previously believed to be particularly secure.
The US intelligence agency NSA has been taking advantage of the smartphone boom. It has developed the ability to hack into iPhones, android devices and even the BlackBerry, previously believed to be particularly secure.
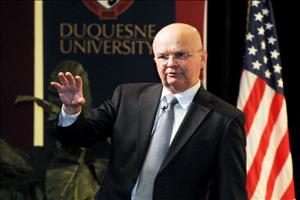
Michael Hayden has an interesting story to tell about the iPhone. He and his wife were in an Apple store in Virginia, Hayden, the former head of the NSA, said at a conference in Washington recently. A salesman approached and raved about the iPhone, saying that there were already "400,000 apps" for the device. Hayden, amused, turned to his wife and quietly asked: "This kid doesn't know who I am, does he? Four-hundred-thousand apps means 400,000 possibilities for attacks."
Read moreU.S., British intelligence mining data from nine U.S. Internet companies in broad secret program
 The National Security Agency and the FBI are tapping directly into the central servers of nine leading U.S. Internet companies, extracting audio and video chats, photographs, e-mails, documents, and connection logs that enable analysts to track foreign targets, according to a top-secret document obtained by The Washington Post.
The National Security Agency and the FBI are tapping directly into the central servers of nine leading U.S. Internet companies, extracting audio and video chats, photographs, e-mails, documents, and connection logs that enable analysts to track foreign targets, according to a top-secret document obtained by The Washington Post.
The program, code-named PRISM, has not been made public until now. It may be the first of its kind.
The NSA prides itself on stealing secrets and breaking codes, and it is accustomed to corporate partnerships that help it divert data traffic or sidestep barriers.
Read more New secured zone of Google Play: secure messenger SafeUM for Android. Download, Install, Communicate
New secured zone of Google Play: secure messenger SafeUM for Android. Download, Install, Communicate
Axarhöfði 14,
110 Reykjavik, Iceland














